To connect your Microsoft Entra ID to Kiro:
- Create Entra application for Kiro
- Configure Entra application
- Create the Kiro Profile
- Set Entra up application provisioning
- Add users and groups to Entra application
First, create a new custom application in Microsoft Entra ID.
From the Microsoft Entra admin center create a new application (Enterprise applications -> New application). From the Microsoft Entra App Gallery select "Create your own application" option
Loading image...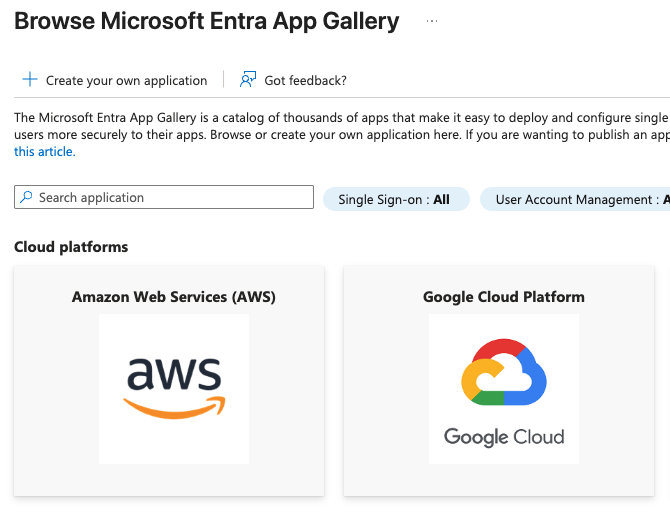
Set a descriptive name, for example, Kiro-Entra. Then, select the "Integrate any other application you don't find in the gallery (Non-gallery)" option for the "What are you looking to do with your application?" field, and select "Create" to create the application.
Loading image...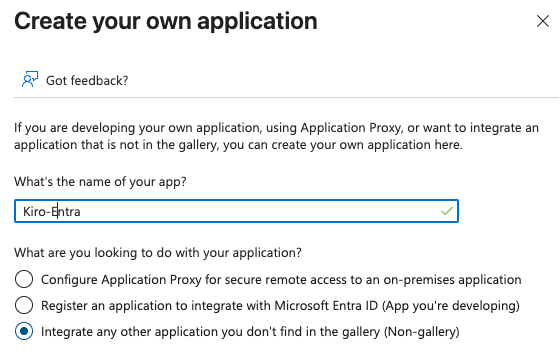
Next, configure the application you have created to allow user identities to present the right authorization to access Kiro.
Next, expose the API endpoint for Kiro to sync user identities.
For the "Kiro-Entra" application (App registrations -> All applications -> Kiro-Entra), select the "Expose an API" option. Select the "Add" link next to the "Application ID URI" field. This will bring up a dialog with a default value for the Application URI. Save it with the default value. Next, you have to add two scopes, that define the permissions that an identity has to present to Kiro for it to successfully respond to requests.
Loading image...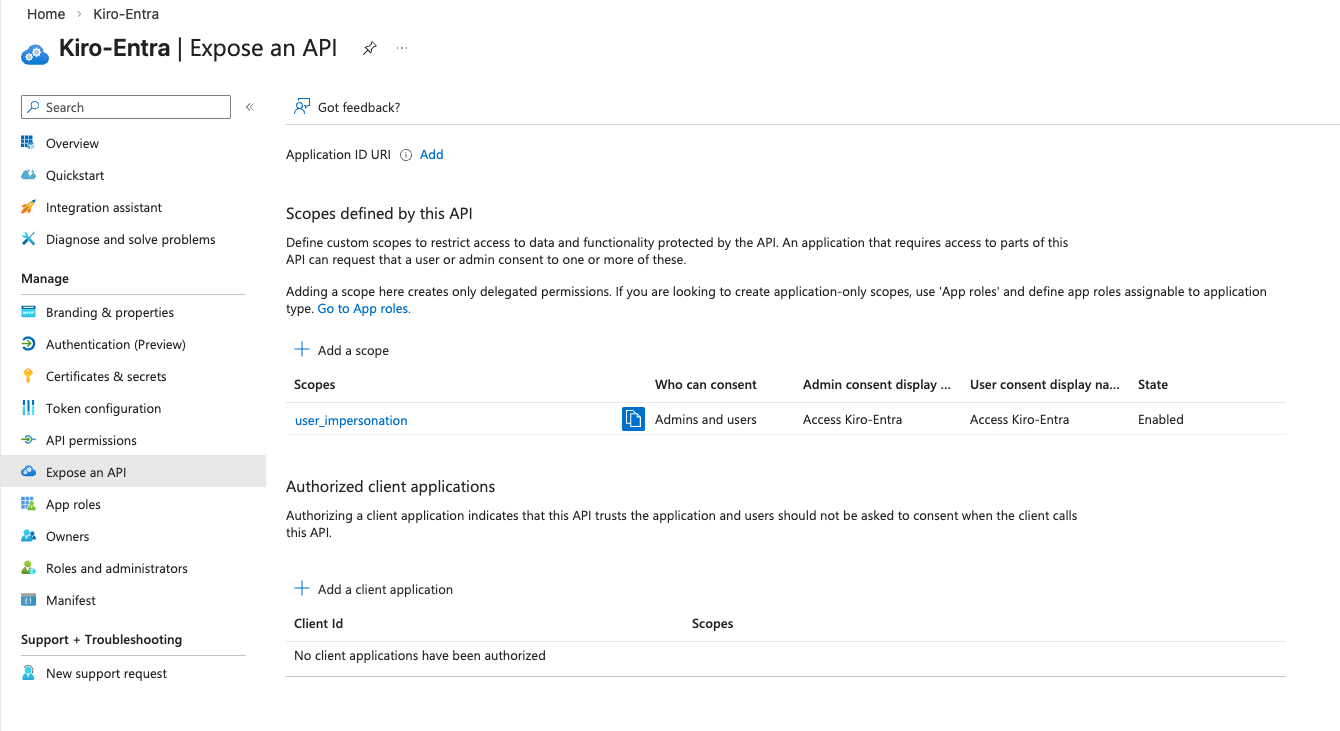
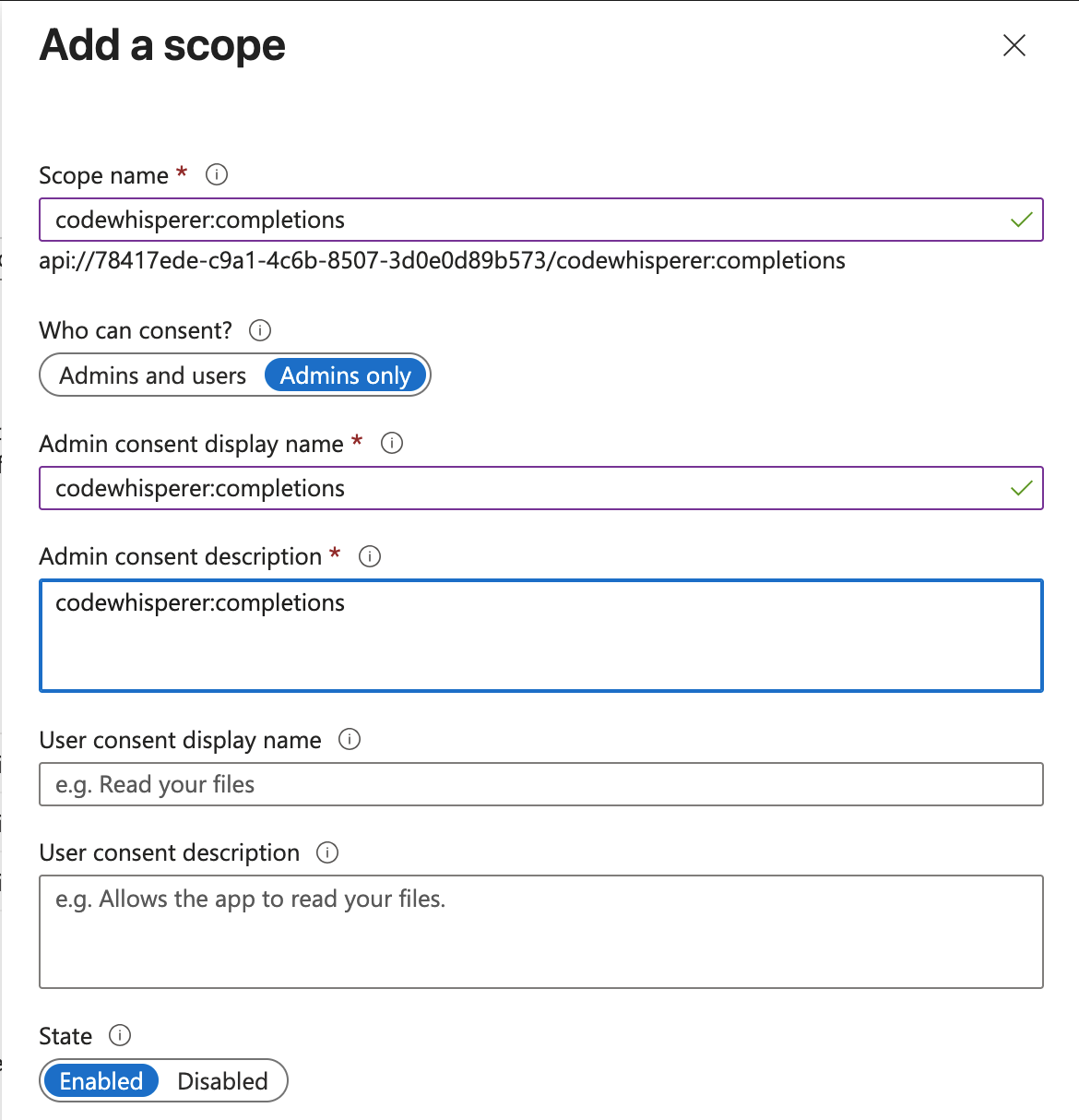
The first scope will enable users to have access to auto complete feature in Kiro by setting the following attributes of the scope:
- Scope Name: codewhisperer:completions
- Who can consent?: Admins and Users
- Admin consent display name: codewhisperer:completions
- Admin consent description: codewhisperer:completions
- State: Enabled
The second scope will enable users to have conversations with Kiro by setting the following attributes of the scope:
- Scope Name: codewhisperer:conversations
- Who can consent?: Admins and Users
- Admin consent display name: codewhisperer:conversations
- Admin consent description: codewhisperer:conversations
- State: Enabled
After you have completed adding the scopes, "Expose an API" page should look like this:
Loading image...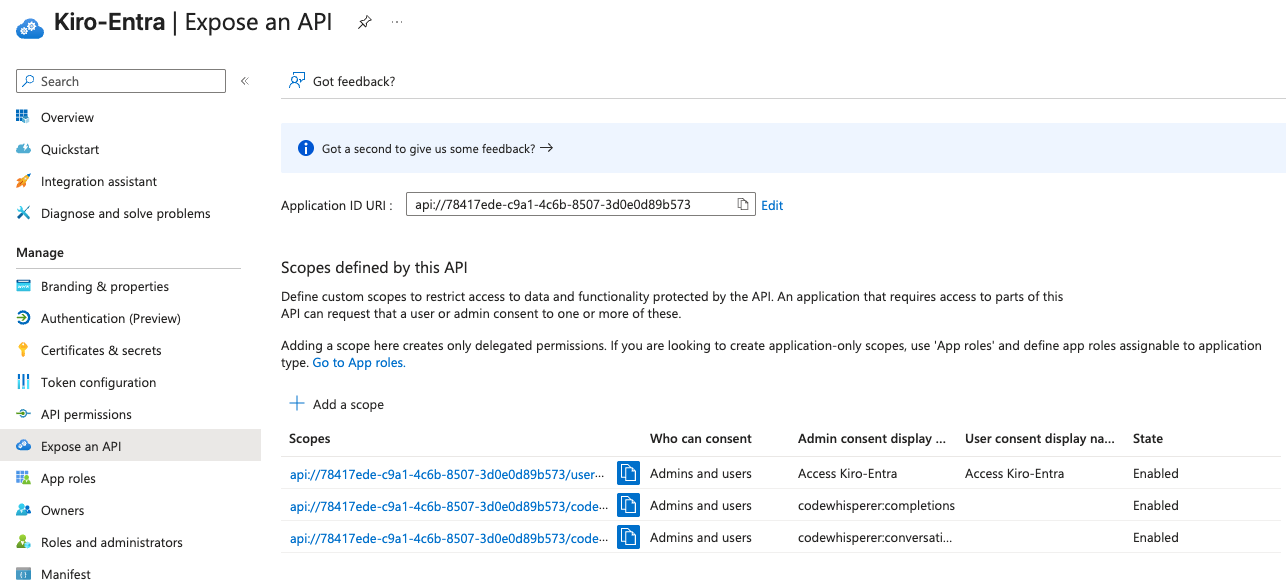
- codewhisperer:completions — Authorizes the user to access the inline code completion feature in Kiro.
- codewhisperer:conversations — Authorizes the user to access the chat and conversation feature in Kiro.
Only grant the scopes that your organization requires. You should understand the impact of each scope when configuring access policies.
In this step, you will configure the URI of the Kiro clients to redirect from Microsoft Entra ID after the user completes authentication process. To do that, select "Authentication (Preview)" option for the Kiro application (example: Kiro-Entra). Select "Add Redirect URI" button and in the platform to set redirect URI select "Mobile and desktop application".
You will add two redirect URIs - one, "kiro://kiro.oauth/callback" and the second, "http://localhost/oauth/callback".
After adding the redirect URIs, the page should look like this:
Loading image...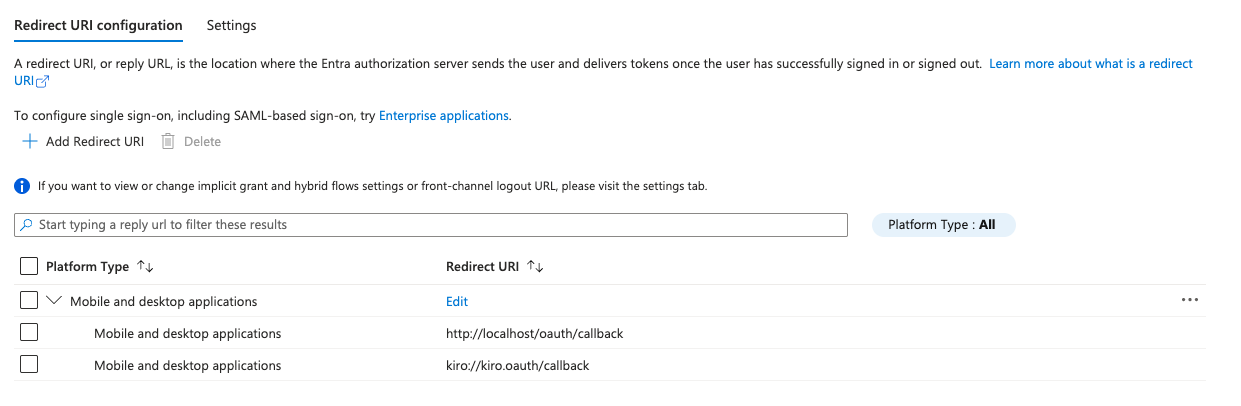
Last, set the version of the access token that Kiro will request. By default, Entra ID uses OAuth 1.0. Kiro expects OAuth 2.0. To do that, set the value of "api" → "requestedAccessTokenVersion" field to 2, and Save.
Loading image...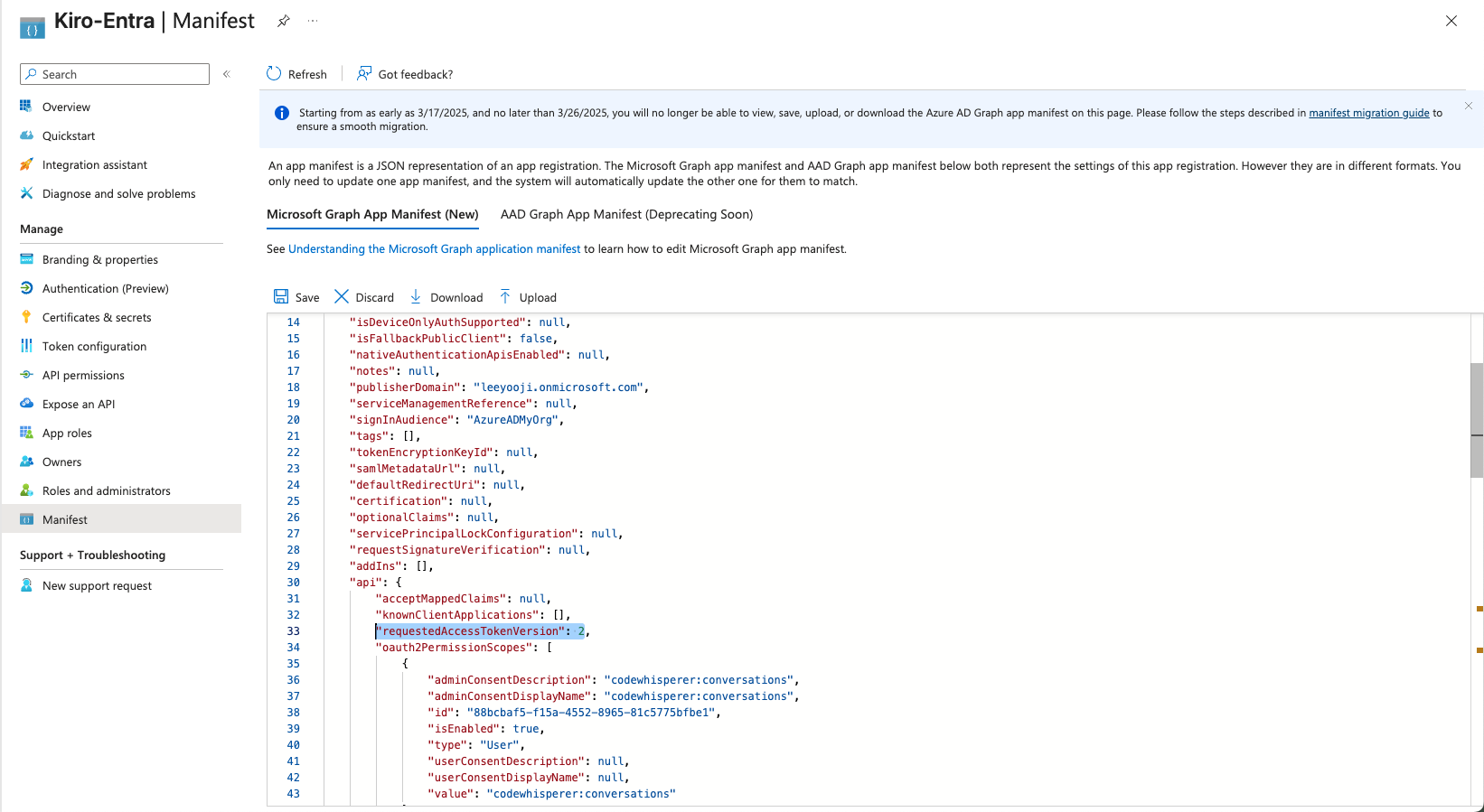
Now, you are ready to set up the Kiro Profile.
Setting up Kiro profile and connecting to your Microsoft Entra ID IdP consists of the following steps:
- Configuration Microsoft Entra ID application properties in Kiro
- Add and verify your domain in Kiro
- Set up provisioning in Microsoft Entra ID
- Verify Connection
In AWS console, navigate to the Kiro console and select "Get started" to set up a Kiro profile. Select "Connect an existing Identity provider" option to connect to Microsoft Entra ID.
Loading image...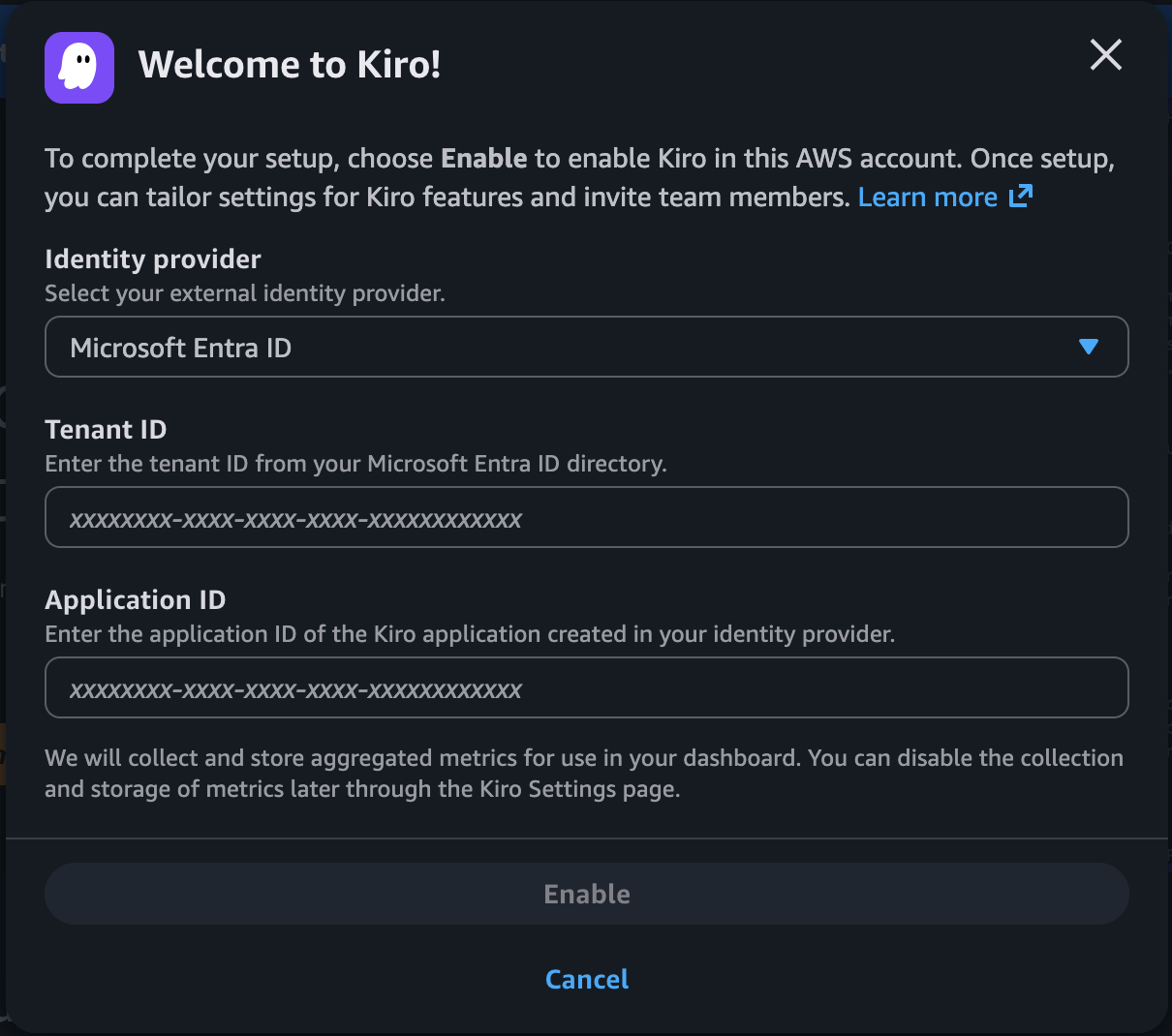
From the left nav in Microsoft Entra, select App registrations -> All applications and select "Kiro-Entra". This will open the "Overview" tab.
Loading image...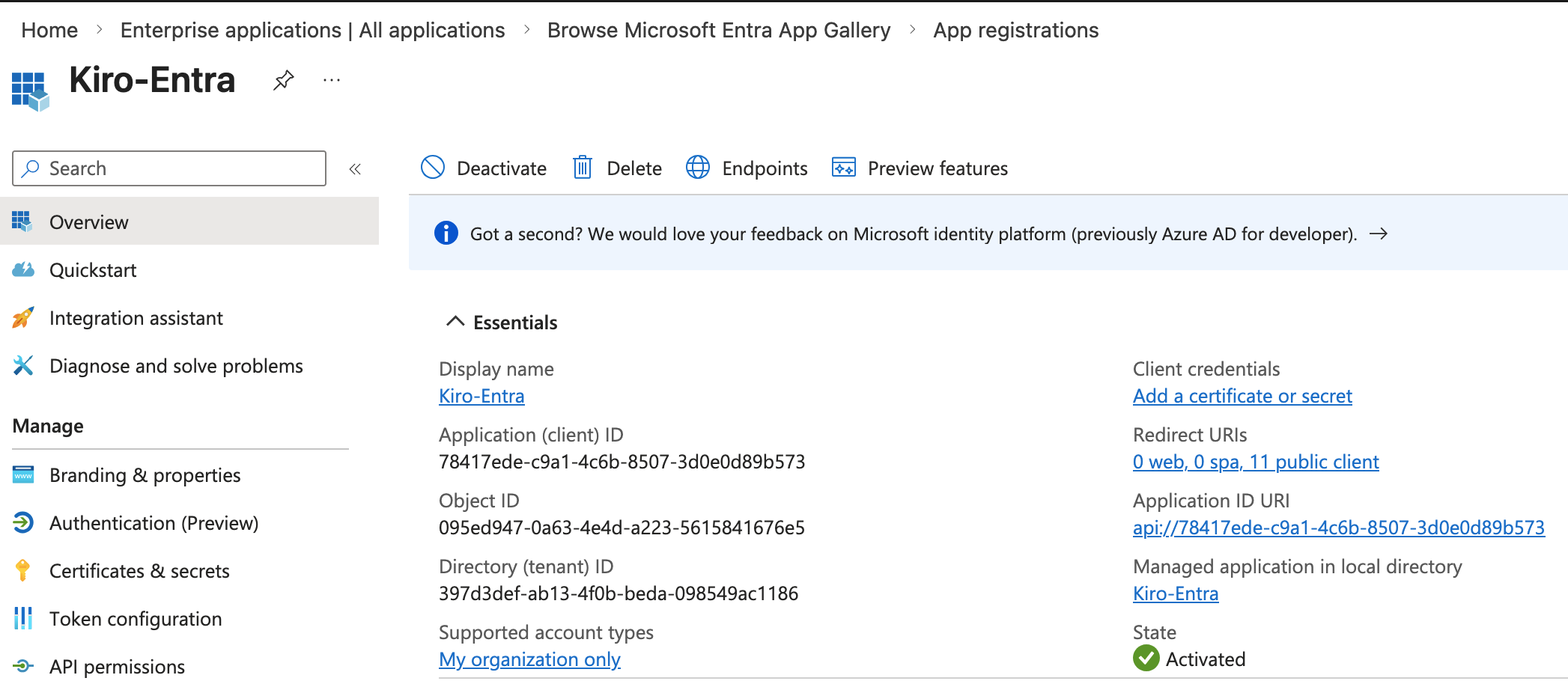
First, copy the "Application (client) id" field value and paste it in the "Application ID" field in the Kiro profile you are creating. Next, copy the value from "Directory (tenant) ID" field and past into the "Tenant ID" field in the Kiro Profile you are creating, and the value from "Application (client) ID" into the "Application ID" field in the Kiro Profile, and select "Create" to create the Profile.
Select the "Settings" button and in the Identity management -> Domains section, select "Add domain" to add your company domain
Loading image...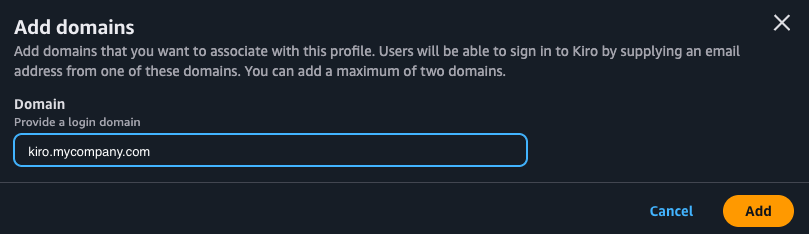
Selecting "Add" will add the domain and show you a verification token. Copy the verification token. The domain added will show up in the Domains list with "Pending" status.
In your DNS Provider like Amazon Route53, create TXT record with that verification token.
Loading image...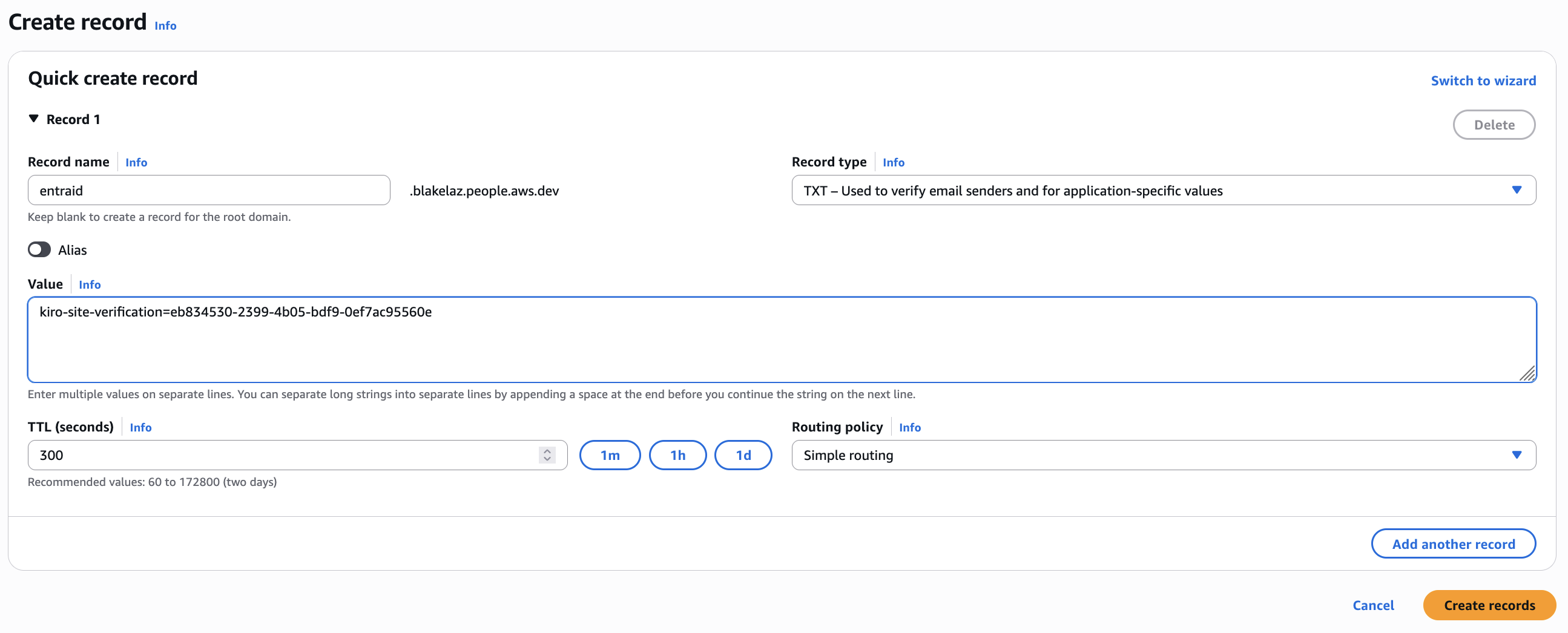
If the configuration is valid, after a few minutes the status will be "Verified".
Loading image...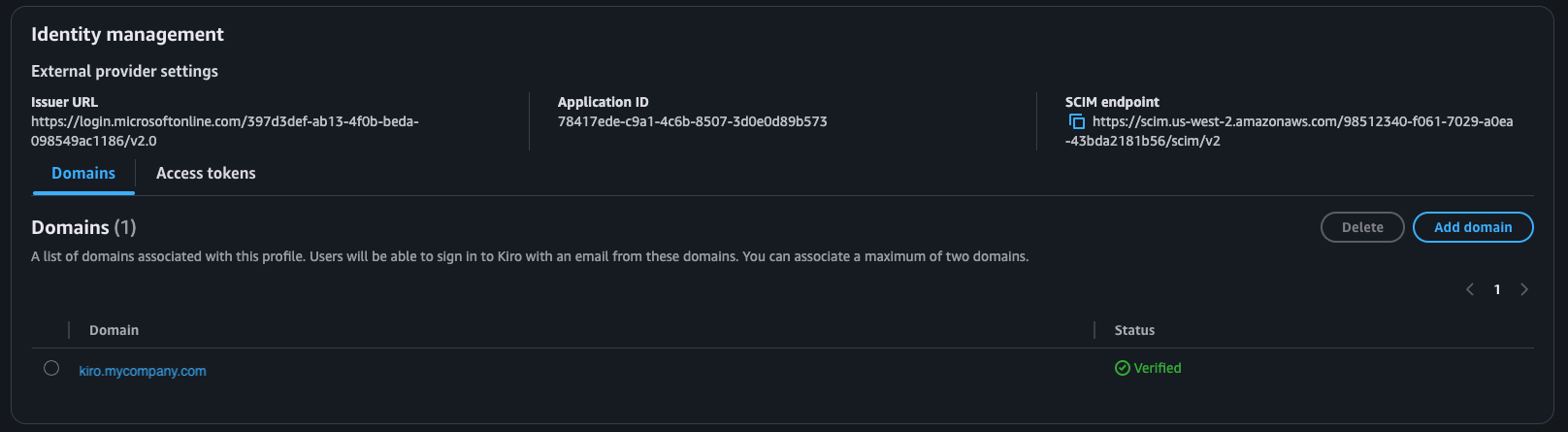
In this step, you will provision the Kiro application and verify that Kiro can sync identities from your Entra ID identity store.
In Entra ID admin console, navigate to Enterprise Apps -> Kiro-Entra -> Provisioning. Select the "Provisioning" link from the side bar to configure the provisioning settings.
First, set the "Provisioning Mode" to Automatic. Next, you have to configure the Tenant URL and Secret token.
Loading image...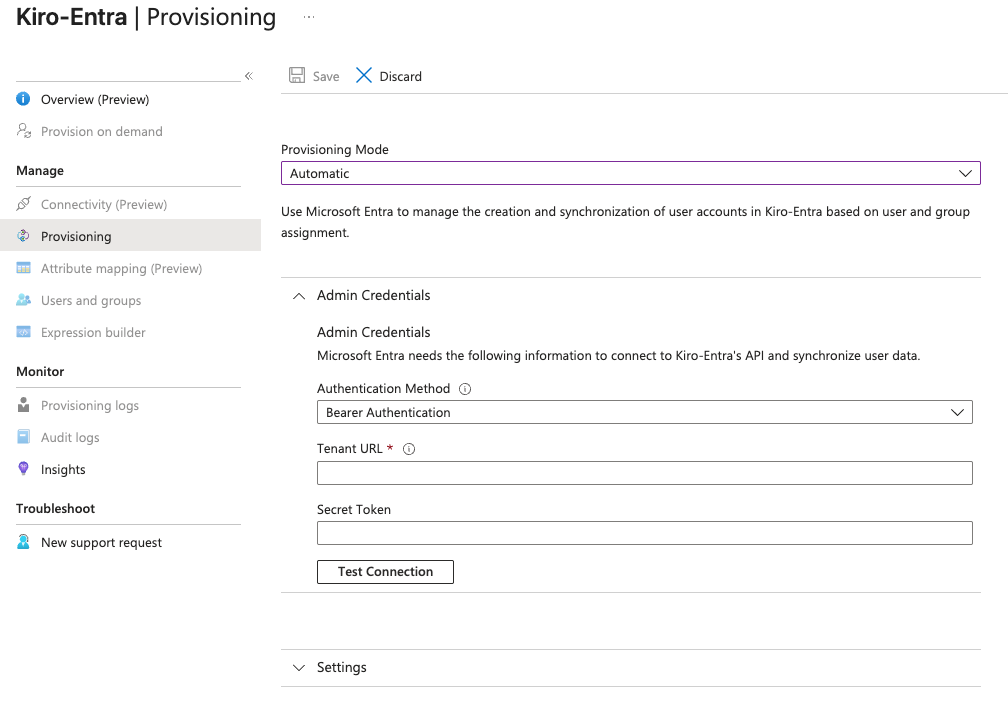
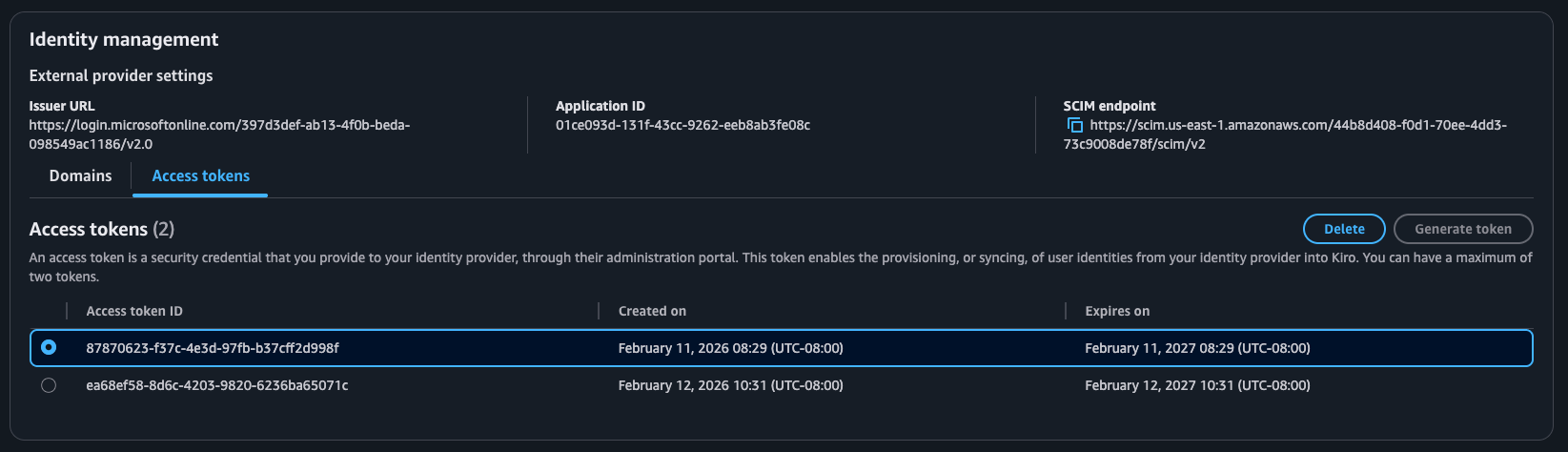
In the Kiro AWS console, navigate to Settings -> Identity Management -> Access Tokens section. Select "Generate Token" to generate an access token. Copy the access token and paste it in the "Secret Token" field in the Provisioning configuration.
Next, from the Settings page of the Kiro profile in the AWS console, copy the value in "SCIM Endpoint" from the "Identity management" section. Paste that in the "Tenant URL" field in the Provisioning configuration in Entra ID. With this, you have set up the secure synchronization of identities to Kiro from Entra ID.
Loading image...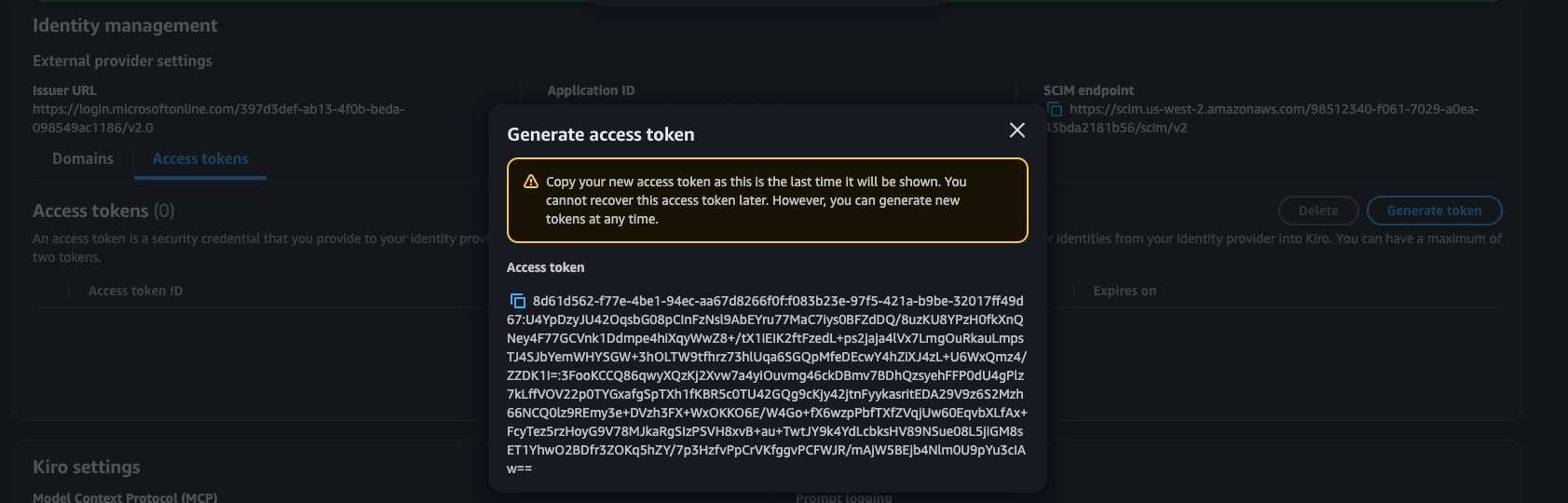
Now select "Test Connection" to validate the configuration. If that is successful, select "Save" to complete the provisioning.
Loading image...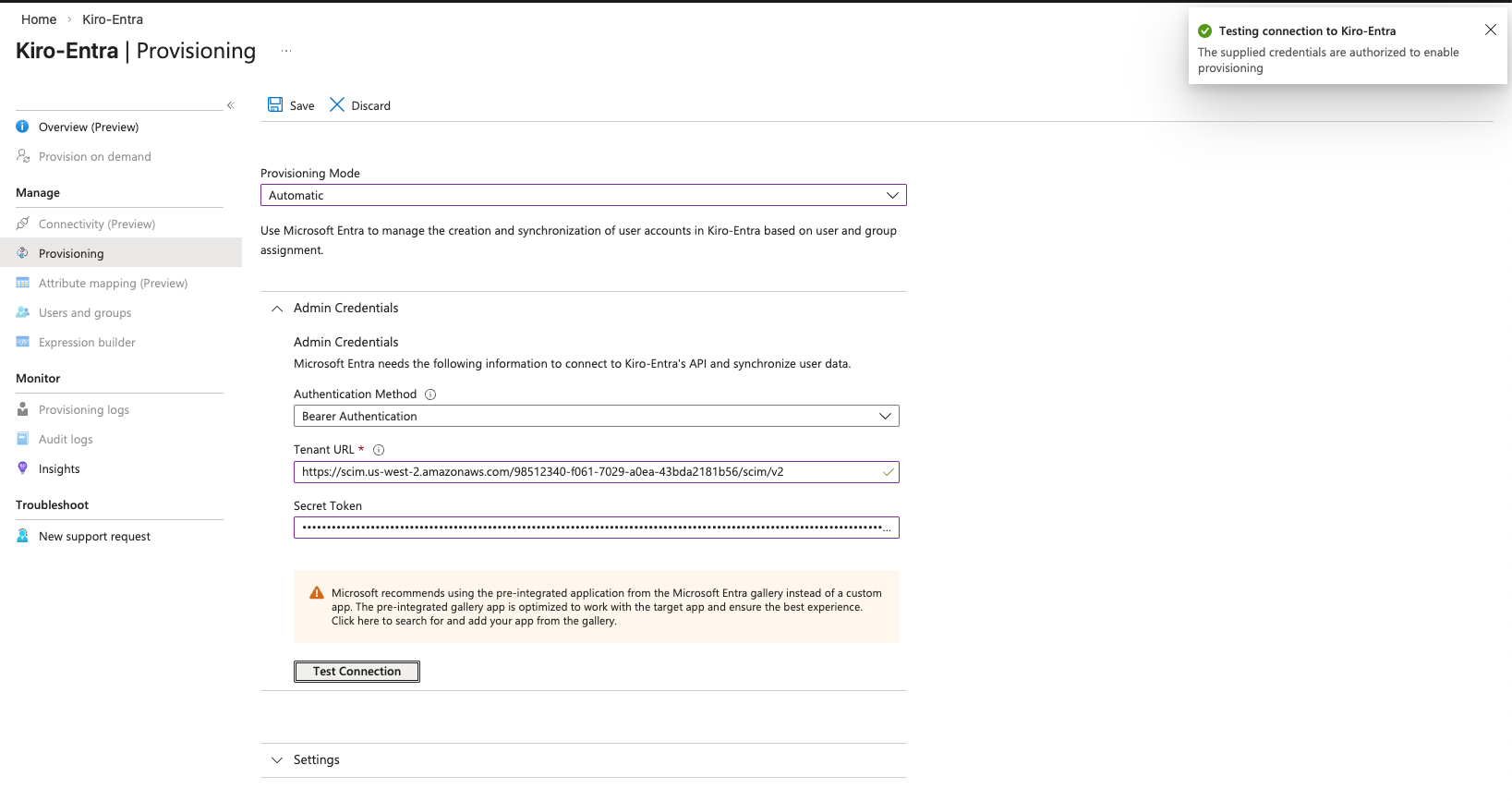
- The access token generated for SCIM provisioning is a long-lived credential. Treat it with the same care as a password.
- SCIM tokens are not automatically rotated. You must manually rotate them according to your organization's credential rotation policy.
- If a token is compromised, revoke it immediately using the revoke button in the Kiro admin console (Settings → Identity Management → Access Tokens), then generate a new token and update it in Entra's provisioning configuration.
IMPORTANT: Refresh the application page in Entra ID.
The sidebar links should be enabled now. To enable users and groups to be synchronized from Entra ID to Kiro, navigate to the "Attribute mapping (Preview)" section. You will see that both Provision Groups and Users are enabled.
Loading image...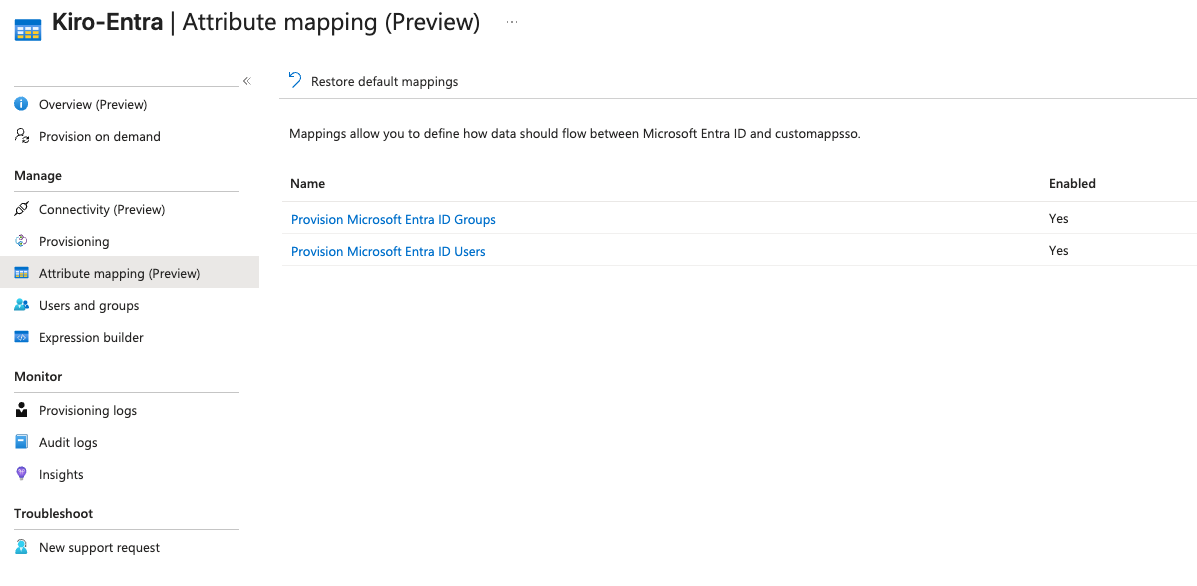
Select the "Provision Microsoft Entra ID Users" link to open the "Attribute Mapping" page. Select the "Edit" button for the "externalId" attribute to open the "Edit Attribute" page. Set the Source attribute value to "objectId" and save the configuration. "objectId" uniquely identifies a user or group and doesn't change, making it easy for Kiro to identify and synchronize users/groups.
Loading image...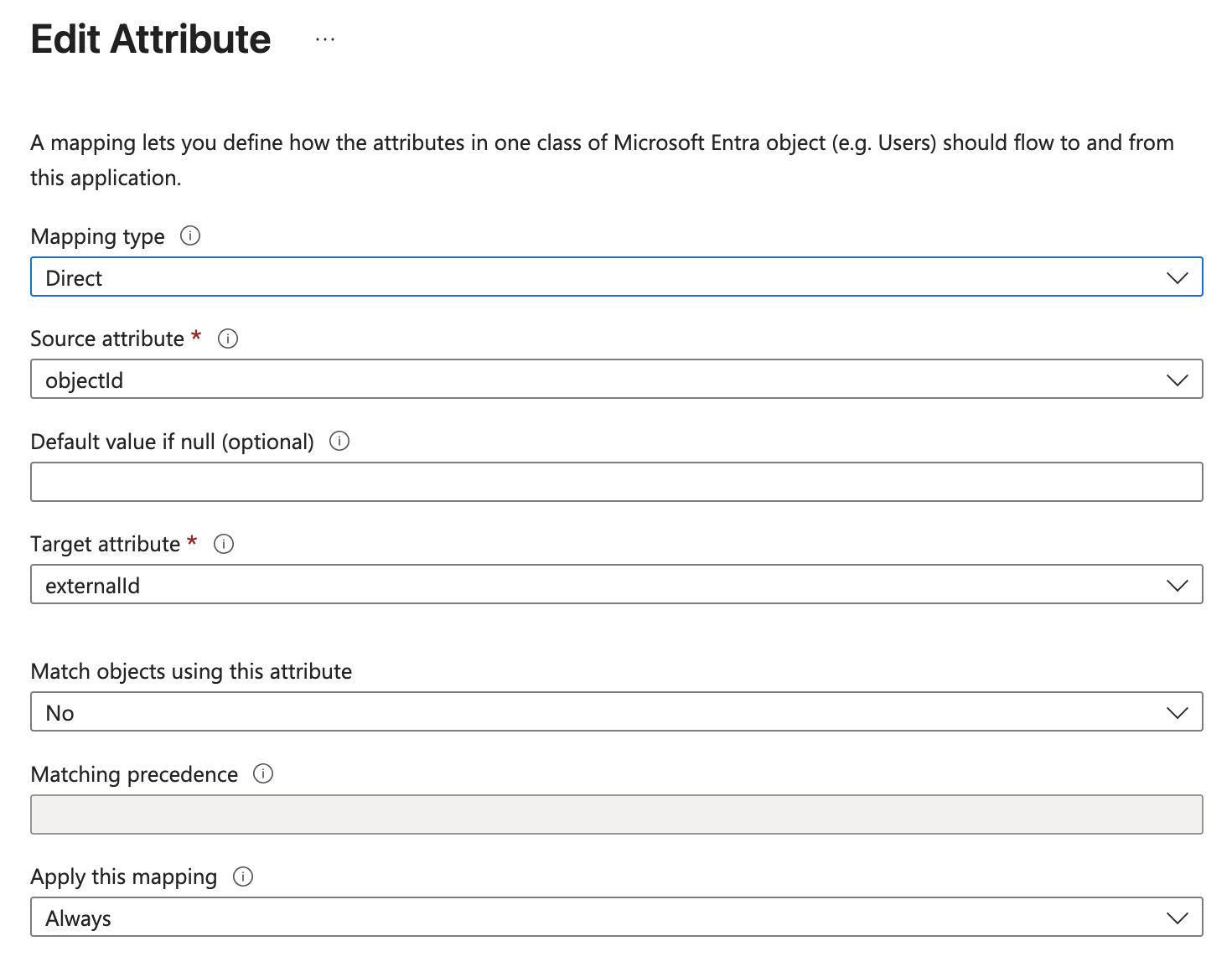
Enterprise User Extension attributes (delete these):
urn:ietf:params:scim:schemas:extension:enterprise:2.0:User:employeeNumberurn:ietf:params:scim:schemas:extension:enterprise:2.0:User:departmenturn:ietf:params:scim:schemas:extension:enterprise:2.0:User:manager
Phone number attributes (delete these):
phoneNumbers[type eq "work"].valuephoneNumbers[type eq "mobile"].valuephoneNumbers[type eq "fax"].value
To remove these attributes, select the attribute row in the mapping table and choose "Delete" for each one listed above. Save the mapping after all unsupported attributes have been removed.
Now that the users and groups can be synchronized from Entra ID application to Kiro, you have to configure which users and groups will be synchronized as part of this application. The selected users and groups will be available to associate with a Kiro subscription in the Kiro profile.
To view users and groups automatically provisioned, navigate to the "Users and groups" section in the Entra ID application. It may take some time for users and groups to appear on their own. Refer to Entra documentation for tracking the progress of the provisioning process.
To manually provision, navigate to "Provisioning" page and select "Provision On Demand" under "Quick Actions" section.
Loading image...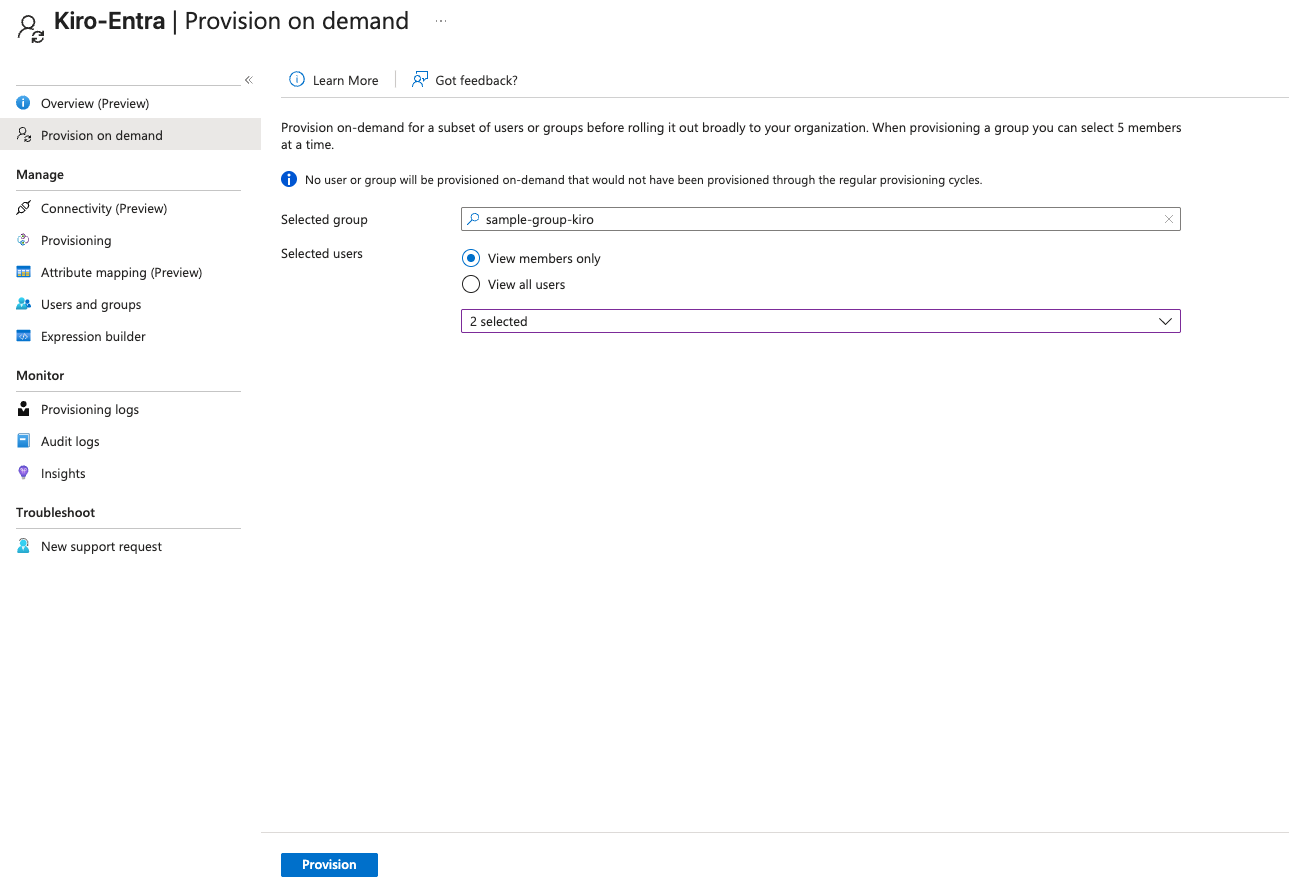
If you are provisioning a group, make sure you select all the users in the group. After you have successfully configured the group and the users in the group, you will see a success screen.
Loading image...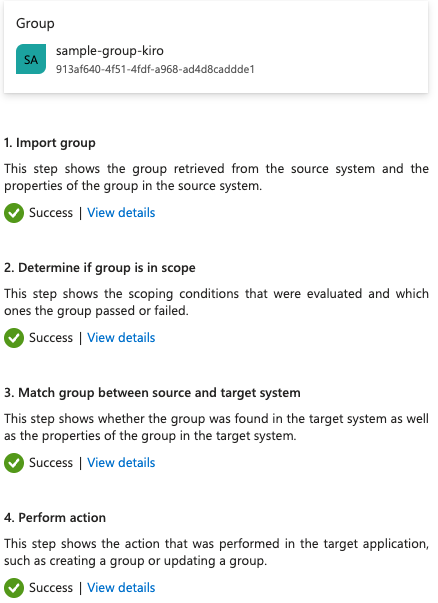
Repeat the steps to add all the users and groups you want to synchronize with Kiro.
You have now completed all the steps required to configure an application in Entra ID, connect the application with a Kiro Profile, and add users/groups to the Profile. You can now start subscribing team members to Kiro.
Session management
- Kiro uses OIDC refresh tokens to maintain user sessions. When a session expires, the refresh token keeps the Kiro session alive independently until the refresh token itself expires.
- You cannot force-revoke active user sessions from the Kiro console. To remove access, you have to remove the user from the Entra application — access will be revoked at the next token refresh attempt.
- Go to Enterprise apps > your application > Users and Groups. Select the user, then remove assignment
Redirect URI security
- Add only the redirect URIs specified in this guide.
Profile deletion warning
If you delete a Kiro profile after provisioning and create a new profile with the same Entra application, group membership will not be synced. You must re-provision the application completely.
Preventing unauthorized access
- Do not add any user to the Kiro application in Entra.
- Verify the user is not a member of any group that is assigned to the Kiro application.
- After creating a group-based subscription, review the Subscriptions tab in the Kiro console to confirm that no unintended users received a subscription.
Removing a user and deprovisioning behavior
- Remove the user's assignment from your Kiro application in Entra. This blocks all future login attempts.
- Existing sessions remain active until the next token refresh is attempted, at which point access is revoked. Active sessions are not immediately terminated.
- Subscription removal is not automatic. After removing a user from the Entra application, you must also manually delete the user's subscription in the Kiro console to release the seat.
Group membership sync behavior
- Kiro relies entirely on push-based SCIM sync from Entra. Kiro cannot request a pull from Entra.
- Group membership changes are pushed approximately every 40 minutes. Admins can trigger an immediate sync by using "Provision on Demand" in the Entra console.
| Missed step | How will this manifest | How to fix | Notes |
|---|---|---|---|
| Did not set access token version to 2 in manifest | After login, API calls will fail with authorization errors | In App registrations, edit the Manifest and set api.requestedAccessTokenVersion to 2 | Entra defaults to OAuth 1.0; Kiro requires OAuth 2.0 |
| Did not set scopes in Expose an API | Login screen will show an error | Add codewhisperer:completions and codewhisperer:conversations scopes in Expose an API | Both scopes are required |
| Did not set attribute mapping in provisioning | After login, user would not have a subscription (API calls fail) | In Attribute Mapping, set externalId source attribute to objectId. Delete ALL subscriptions and re-provision. | objectId is the stable unique identifier |
| Did not set redirect URIs | Login attempts show an error screen | Add the required localhost redirect URIs in Authentication settings | See the setup guide for the full list of ports |
| Did not provision on demand | Users/groups do not appear in the Kiro console | Navigate to Provisioning and select "Provision on Demand" | Automatic sync can take up to 40 minutes |
| Deleted profile after provisioning, created new profile with same app | Group membership is not synced | Re-provision the application from scratch with a new SCIM token | See Profile deletion warning above |
Connect your Microsoft Entra ID IdP